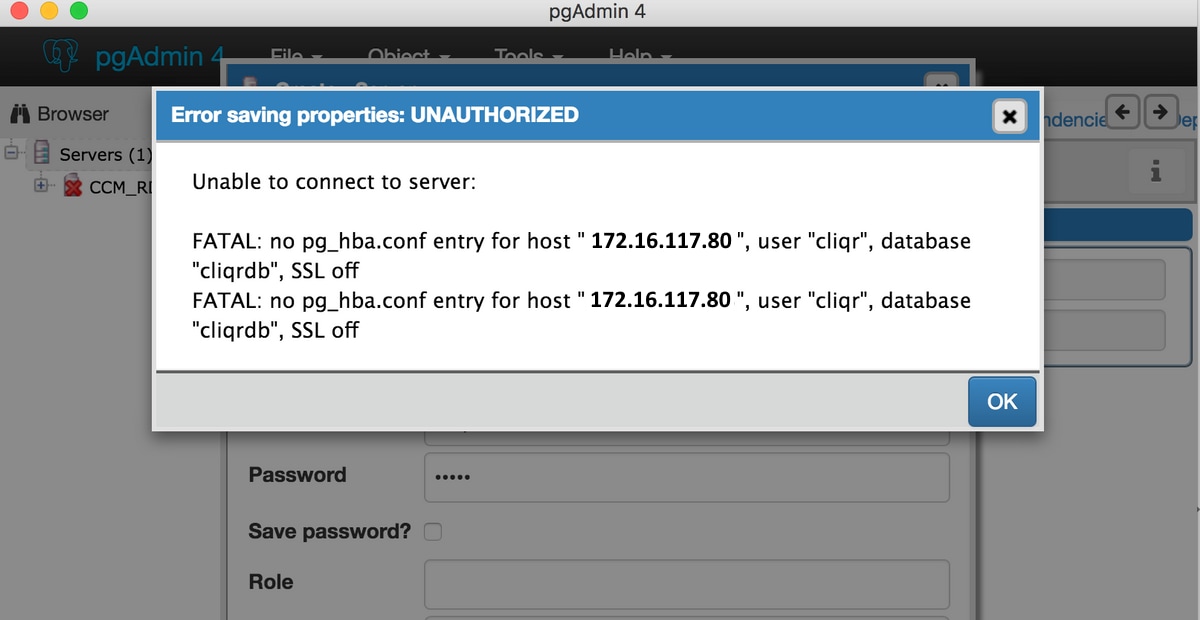
No Pg Hba.conf Entry For Host
Client authentication is controlled by a configuration file, which traditionally is named pg_hba.conf and is stored in the database cluster's data directory. (HBA stands for host-based authentication.) A default pg_hba.conf file is installed when the data directory is initialized by initdb. It is possible to place the authentication configuration file elsewhere, however; see the hba_file configuration parameter.
361. This is the first point where we have access to the hba record for the. Any idea how to repopulate pghba.conf file in Tableau 2018.3.0 version. If so, please give me the commands If so, please give me the commands Like Show 0 Likes (0).
The general format of the pg_hba.conf file is a set of records, one per line. Blank lines are ignored, as is any text after the # comment character. Records cannot be continued across lines. A record is made up of a number of fields which are separated by spaces and/or tabs. Fields can contain white space if the field value is double-quoted. Quoting one of the keywords in a database, user, or address field (e.g., all or replication) makes the word lose its special meaning, and just match a database, user, or host with that name.
Each record specifies a connection type, a client IP address range (if relevant for the connection type), a database name, a user name, and the authentication method to be used for connections matching these parameters. The first record with a matching connection type, client address, requested database, and user name is used to perform authentication. There is no “fall-through” or “backup”: if one record is chosen and the authentication fails, subsequent records are not considered. If no record matches, access is denied.
A record can have one of the seven formats
The meaning of the fields is as follows:
localThis record matches connection attempts using Unix-domain sockets. Without a record of this type, Unix-domain socket connections are disallowed.
hostThis record matches connection attempts made using TCP/IP. host records match either SSL or non-SSL connection attempts.
Note
Remote TCP/IP connections will not be possible unless the server is started with an appropriate value for the listen_addresses configuration parameter, since the default behavior is to listen for TCP/IP connections only on the local loopback address localhost.
X-Force Adobe CS6 Master Collection Keygen All Comments Here we have the last Patcher by PainteR for all Adobe CC Softwares, this Patcher simply replace the amtlib.dll file for the cracked version. Adobe Master Collection Cs6 X-force Keygen Not Working Adobe Creative Suite 6 Master Collection software delivers unprecedented performance with blazing-fast 64-bit native support and GPU acceleration.Groundbreaking new creative tools provide innovative ways to design for the latest devices. X-force adobe cs6 master collection keygen generator. Adobe Photoshop allows you to create adobe cs6 master collection xforce keygen images and edit them. Photoshop used to create photorealistic images to work with color scanned images, retouching, color correction, transformation of graphs, color separation, etc. Adobe Photoshop has all the methods of working with bitmaps, in this case is to work with layers and uses contours.
hostsslThis record matches connection attempts made using TCP/IP, but only when the connection is made with SSL encryption.
To make use of this option the server must be built with SSL support. Furthermore, SSL must be enabled by setting the ssl configuration parameter (see Section 18.9 for more information). Otherwise, the hostssl record is ignored except for logging a warning that it cannot match any connections.
hostnosslThis record type has the opposite behavior of hostssl; it only matches connection attempts made over TCP/IP that do not use SSL.
databaseSpecifies which database name(s) this record matches. The value all specifies that it matches all databases. The value sameuser specifies that the record matches if the requested database has the same name as the requested user. The value samerole specifies that the requested user must be a member of the role with the same name as the requested database. (samegroup is an obsolete but still accepted spelling of samerole.) Superusers are not considered to be members of a role for the purposes of samerole unless they are explicitly members of the role, directly or indirectly, and not just by virtue of being a superuser. The value replication specifies that the record matches if a physical replication connection is requested (note that replication connections do not specify any particular database). Otherwise, this is the name of a specific PostgreSQL database. Multiple database names can be supplied by separating them with commas. A separate file containing database names can be specified by preceding the file name with @.
userSpecifies which database user name(s) this record matches. The value all specifies that it matches all users. Otherwise, this is either the name of a specific database user, or a group name preceded by +. (Recall that there is no real distinction between users and groups in PostgreSQL; a + mark really means “match any of the roles that are directly or indirectly members of this role”, while a name without a + mark matches only that specific role.) For this purpose, a superuser is only considered to be a member of a role if they are explicitly a member of the role, directly or indirectly, and not just by virtue of being a superuser. Multiple user names can be supplied by separating them with commas. A separate file containing user names can be specified by preceding the file name with @.
addressSpecifies the client machine address(es) that this record matches. This field can contain either a host name, an IP address range, or one of the special key words mentioned below.
An IP address range is specified using standard numeric notation for the range's starting address, then a slash (/) and a CIDR mask length. The mask length indicates the number of high-order bits of the client IP address that must match. Bits to the right of this should be zero in the given IP address. There must not be any white space between the IP address, the /, and the CIDR mask length.
Typical examples of an IPv4 address range specified this way are 172.20.143.89/32 for a single host, or 172.20.143.0/24 for a small network, or 10.6.0.0/16 for a larger one. An IPv6 address range might look like ::1/128 for a single host (in this case the IPv6 loopback address) or fe80::7a31:c1ff:0000:0000/96 for a small network. 0.0.0.0/0 represents all IPv4 addresses, and ::0/0 represents all IPv6 addresses. To specify a single host, use a mask length of 32 for IPv4 or 128 for IPv6. In a network address, do not omit trailing zeroes.
An entry given in IPv4 format will match only IPv4 connections, and an entry given in IPv6 format will match only IPv6 connections, even if the represented address is in the IPv4-in-IPv6 range. Note that entries in IPv6 format will be rejected if the system's C library does not have support for IPv6 addresses.
You can also write all to match any IP address, samehost to match any of the server's own IP addresses, or samenet to match any address in any subnet that the server is directly connected to.
If a host name is specified (anything that is not an IP address range or a special key word is treated as a host name), that name is compared with the result of a reverse name resolution of the client's IP address (e.g., reverse DNS lookup, if DNS is used). Host name comparisons are case insensitive. If there is a match, then a forward name resolution (e.g., forward DNS lookup) is performed on the host name to check whether any of the addresses it resolves to are equal to the client's IP address. If both directions match, then the entry is considered to match. (The host name that is used in pg_hba.conf should be the one that address-to-name resolution of the client's IP address returns, otherwise the line won't be matched. Some host name databases allow associating an IP address with multiple host names, but the operating system will only return one host name when asked to resolve an IP address.)
A host name specification that starts with a dot (.) matches a suffix of the actual host name. So .example.com would match foo.example.com (but not just example.com).
When host names are specified in pg_hba.conf, you should make sure that name resolution is reasonably fast. It can be of advantage to set up a local name resolution cache such as nscd. Also, you may wish to enable the configuration parameter log_hostname to see the client's host name instead of the IP address in the log.
This field only applies to host, hostssl, and hostnossl records.
Note
Users sometimes wonder why host names are handled in this seemingly complicated way, with two name resolutions including a reverse lookup of the client's IP address. This complicates use of the feature in case the client's reverse DNS entry is not set up or yields some undesirable host name. It is done primarily for efficiency: this way, a connection attempt requires at most two resolver lookups, one reverse and one forward. If there is a resolver problem with some address, it becomes only that client's problem. A hypothetical alternative implementation that only did forward lookups would have to resolve every host name mentioned in pg_hba.conf during every connection attempt. That could be quite slow if many names are listed. And if there is a resolver problem with one of the host names, it becomes everyone's problem.
Also, a reverse lookup is necessary to implement the suffix matching feature, because the actual client host name needs to be known in order to match it against the pattern.
Note that this behavior is consistent with other popular implementations of host name-based access control, such as the Apache HTTP Server and TCP Wrappers.
IP-addressIP-maskThese two fields can be used as an alternative to the IP-address/mask-length notation. Instead of specifying the mask length, the actual mask is specified in a separate column. For example, 255.0.0.0 represents an IPv4 CIDR mask length of 8, and 255.255.255.255 represents a CIDR mask length of 32.
These fields only apply to host, hostssl, and hostnossl records.
auth-methodSpecifies the authentication method to use when a connection matches this record. The possible choices are summarized here; details are in Section 20.3.
trustAllow the connection unconditionally. This method allows anyone that can connect to the PostgreSQL database server to login as any PostgreSQL user they wish, without the need for a password or any other authentication. See Section 20.3.1 for details.
rejectReject the connection unconditionally. This is useful for “filtering out” certain hosts from a group, for example a reject line could block a specific host from connecting, while a later line allows the remaining hosts in a specific network to connect.
scram-sha-256Perform SCRAM-SHA-256 authentication to verify the user's password. See Section 20.3.2 for details.
md5Perform SCRAM-SHA-256 or MD5 authentication to verify the user's password. See Section 20.3.2 for details.
passwordRequire the client to supply an unencrypted password for authentication. Since the password is sent in clear text over the network, this should not be used on untrusted networks. See Section 20.3.2 for details.
gssUse GSSAPI to authenticate the user. This is only available for TCP/IP connections. See Section 20.3.3 for details.
sspiUse SSPI to authenticate the user. This is only available on Windows. See Section 20.3.4 for details.
identObtain the operating system user name of the client by contacting the ident server on the client and check if it matches the requested database user name. Ident authentication can only be used on TCP/IP connections. When specified for local connections, peer authentication will be used instead. See Section 20.3.5 for details.
peerObtain the client's operating system user name from the operating system and check if it matches the requested database user name. This is only available for local connections. See Section 20.3.6 for details.
ldapAuthenticate using an LDAP server. See Section 20.3.7 for details.
radiusAuthenticate using a RADIUS server. See Section 20.3.8 for details.
certAuthenticate using SSL client certificates. See Section 20.3.9 for details.
pamAuthenticate using the Pluggable Authentication Modules (PAM) service provided by the operating system. See Section 20.3.10 for details.
bsdAuthenticate using the BSD Authentication service provided by the operating system. See Section 20.3.11 for details.
auth-optionsAfter the auth-method field, there can be field(s) of the form name=value that specify options for the authentication method. Details about which options are available for which authentication methods appear below.
In addition to the method-specific options listed below, there is one method-independent authentication option clientcert, which can be specified in any hostssl record. When set to 1, this option requires the client to present a valid (trusted) SSL certificate, in addition to the other requirements of the authentication method.
Files included by @ constructs are read as lists of names, which can be separated by either whitespace or commas. Comments are introduced by #, just as in pg_hba.conf, and nested @ constructs are allowed. Unless the file name following @ is an absolute path, it is taken to be relative to the directory containing the referencing file.
Since the pg_hba.conf records are examined sequentially for each connection attempt, the order of the records is significant. Typically, earlier records will have tight connection match parameters and weaker authentication methods, while later records will have looser match parameters and stronger authentication methods. Download nginx for mac high sierra 2017. For example, one might wish to use trust authentication for local TCP/IP connections but require a password for remote TCP/IP connections. In this case a record specifying trust authentication for connections from 127.0.0.1 would appear before a record specifying password authentication for a wider range of allowed client IP addresses.
The pg_hba.conf file is read on start-up and when the main server process receives a SIGHUP signal. If you edit the file on an active system, you will need to signal the postmaster (using pg_ctl reload, calling the SQL function pg_reload_conf(), or using kill -HUP) to make it re-read the file.
Note
The preceding statement is not true on Microsoft Windows: there, any changes in the pg_hba.conf file are immediately applied by subsequent new connections.
The system view pg_hba_file_rules can be helpful for pre-testing changes to the pg_hba.conf file, or for diagnosing problems if loading of the file did not have the desired effects. Rows in the view with non-null error fields indicate problems in the corresponding lines of the file.
Tip
To connect to a particular database, a user must not only pass the pg_hba.conf checks, but must have the CONNECT privilege for the database. If you wish to restrict which users can connect to which databases, it's usually easier to control this by granting/revoking CONNECT privilege than to put the rules in pg_hba.conf entries.
Some examples of pg_hba.conf entries are shown in Example 20.1. See the next section for details on the different authentication methods.
Example 20.1. Example pg_hba.conf Entries
pg_hba.conf is configured to allow connections only from the pc the
database is installed on initially. Only one login account exists by
default after a new installation and that is the postgres account.
Until you connect to the db the first time using the postgres account
and create new users accounts will you have the option of using your
Owner account.
For connecting from another windows pc other than the one postgres is
running on the default postgresql.conf file must be modified before
modifying pg_hba.conf. Within postgresql.conf there is an entry
commented out, tcpip_socket = false, uncomment that line and change it
to equal true.
Now you can modify the pg_hba.conf. Add a new line to that reads the
following:
host all all XXX 255.255.255.255 trust
XXX = the ip address of the computer that your application is running
on. If your ip address is say 192.168.123.250 it is ok to enter it in
pg_hba.conf as 192.168.123.0. The .0 acts a wildcard in case your
computer is assigned a new ip address at a later time (hopefully it will
be in the same range as the original..)
Once the above is done you can reboot the computer to stop and restart
postgres.
Before using your application to connect to postgres might I suggest
that you use pgadminIII to connect to it first. PgadminIII is a
graphical program specifically designed to access postgres, create users
/ tables / databases, issue commands etc. A graphical program can save
you the trouble of having to learn some of the sql. PgAdminIII can be
downloaded freely from http://www.pgadmin.org If you choose this the
new connection to create within pgadmin would use a login of postgres,
select the trusted connection box, and you should connect.
Once the above is done with or without getting pgadminIII then modify
your windows ODBC connection to use the postgres account.
The userid would be postgres. No password would be needed. Your ODBC
connection will require a name of a database to connect to initially
however. The only one that exists by default is template1. Template1
is a system database and not to be used to store your applications data
in. You really should create another database within postgres that your
application will write to. You can use pgadminIII to do that with a few
clicks.
Hope that helps.
There are some books on postgresql out there that you can get which
might help as well.
In addition there is a mailing list on www.postgresql.org specifically
for novice users which might help as well.
Mike
On Sat, 2004-06-19 at 05:47, - Barry - wrote:
> This is in part a diary entry, since I'm no longer so enthused or optimistic
> about getting this to work, or whether it's practical for me.
>
> I reread some instructions I got on this list, and decided to give them a
> try. I configured Windows for an ODBC connection, possibly correctly. From
> the very start, it wasn't clear to me which user's account information
> needed to be used and altered, the Owner's or postgres's. The file pg_hba
> seemed to be configured to allow everything, according to the docs, so I
> didn't change it, but I got the fatal 'no pg_hba.config entry' error. Then I
> tried creating a pg_hba.config file for the Owner's account, which I intend
> to access the database from. After I rebooted, permission was denied for the
> whole /var/postgresql/ folder for the user Owner, and I still got the fatal
> error. Then I went to the postgres user's account and saw that my edits to
> pg_hba.config weren't there, but I was able to edit the file, so I did. I
> rebooted, and still got the fatal error from both accounts.
>
> The only edit I made to /var/postgresql/ was to replace the '127.0.0.1' from
> 'host all all 127.0.0.1 255.255.255.255 trust'
> with the IP address I saw in the error message. Maybe I needed to replace
> the mask too, but the only mask I saw at the command line was a subnet mask
> (255.255.255.0), not an IP-mask. In fact, I think there were two different
> ones, along with two different IP Addresses. I used the one under 'Ethernet
> adapter local area connection.' The other title and entries aren't there at
> the moment for some reason.
>
> Still seems like this should be easier. Since this is for a product I might
> sell, I think I should be looking at something more commercial that includes
> an installer to make it easier for others, even if I myself am masochistic.
> More likely, I'll use flat files. Wouldn't be so bad for my purposes anyway.
>
>
> ---------------------------(end of broadcast)---------------------------
> TIP 1: subscribe and unsubscribe commands go to majordomo(at)postgresql(dot)org